Equipment List
Below are the devices used by Dr. Horton. There might be much better equipment out there, so compare products to find the most suitable for your purposes.
The device recommended to detect attacks is the small radiation detector EMFields Acousticom 2 and the HF 35C. The spectrum analyser Aaronia HF-4040 is for more advanced analysis of the frequency distribution. Each of these devices measures different aspects of the attacks.
To detect implants people had success using the Aceco FC6002MKII. Eye implants can be detected using a UV torch.
Please note: The product links are mostly Amazon referral links. If you decide to purchase the device and use the link provided here the advertising reward is awarded to Dr. Horton to be used for funding the investigation with no extra costs to you. This is an easy way to support the investigation. (You remain anonymous as a buyer and Dr. Horton cannot track your purchases.)
Gadgets
- Logbooks
- Audio Recorder
- Telephone Pickup Microphone
- Digital Camera
- Power Bank
- Dash Cam
- Action Cam
- Webcam
Shielding
Security
Measurement
- Electromagnetic Radiation Meter (DEW Attacks)
- Directional Radiation Meter (Sources)
- Radiation Spectrum Analyser
- Bug Detector (RF Body Chips)
- Frequency Counter (Body Chip Frequencies) WANTED!!!
- Thermal Camera (Body Implants, Weapons)
- UV Torch (Eye Implants, Contamination)
- Geiger Counter (Radioactivity, X-Ray Surveillance)
- Gas Detector (Gas Poisoning) WANTED!!!
Data Collection
Logbooks
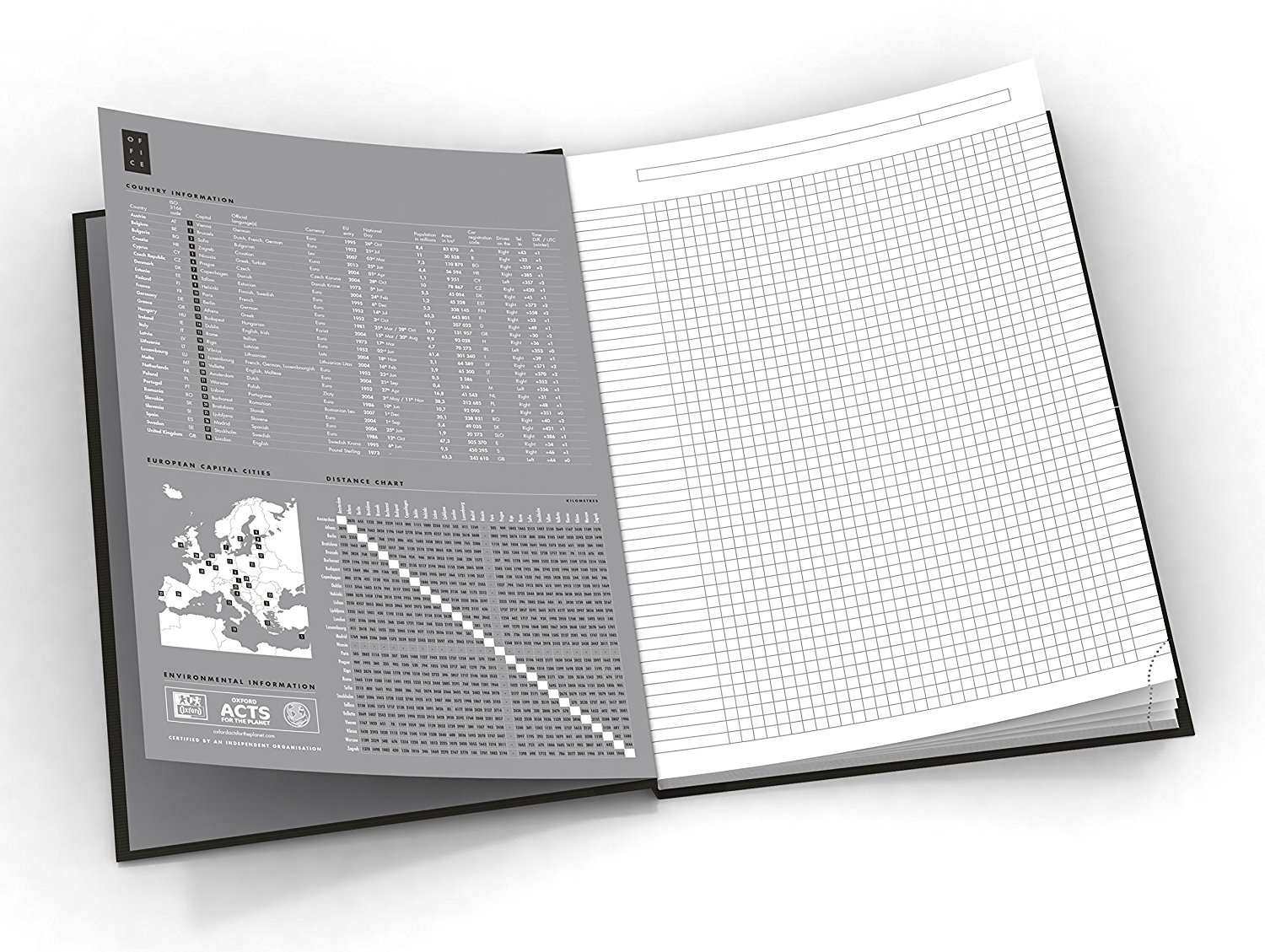 |
25 USD for 4 books from US vendor 23 GBP for 5 books from UK vendor 38 EUR for 5 books from German vendor |
- $2 – $8
- Use bound books, not wire-bound pages that can be removed.
- Number each page. Quickest way is to number the front of the right hand page as 1,3,5,7 etc.
- Note down attacks, symptoms, V2K abuse and threats every day.
- Your handwriting authenticates the document.
- Write the date on every page and write the time of the incident, symptom or attack.
- Number the logbooks in series and photograph them, so that can prove if some disappear.
- Use a type of ink that cannot be erased, for example ball point pen and not ink or pencils.
Logbooks are vital because they document the abuse over long periods of time, can assist your memory for court cases and can themselves be used as evidence in court cases. It can be very tough to write up what happens day by day and you might not always have the time or emotional strength. Nevertheless, it is important to maintain the discipline and do it regularly because it is top class evidence for court cases and can translate into millions of dollars in damage payments for you and your family. If you miss out a number of days or weeks, simply start writing into your logbook again and continue documenting what you can. Logbooks do not have to be complete or daily for them to be used as powerful evidence in court.
You can also note down the existence of photographs, data files, videos or audio recordings. That way if the data files disappear or are deleted you still have an entry about their existence or content.
It is recommended to get bound logbooks like the one shown above which allow you to write a date at the top and the times of the offences or other special marks and highlights in a column on the side of the page. Using such an index, lots of pages can be scanned quickly for relevant information.
You can also regularly scan or photograph your logbook to create a digital copy. However, it is of utmost importance that you also generate hard-copy evidence in your own handwriting in logbooks in addition to digital data. That is because your handwriting is very hard to forge and your logbook cannot be hacked remotely by the intelligence agencies. Don’t worry if a book is stolen, it can be requested back as the Intelligence Agencies collect items and rarely throw something away.
Audio Recorder
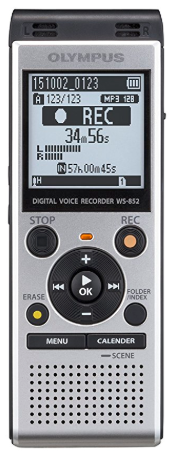 |
44 USD from US vendor 56 GBP from UK vendor 51 EUR from German vendor |
- $30 – $50
- 4GB internal memory at least (storage for many hours of audio)
- microSD slot for extra memory is optional and not necessary as 4GB of internal memory is already a lot and regular backups to another storage device should be done in any case. (Save the microSD for video recording devices where it is essential due to the file sizes.)
- USB connector for data transfer and backup to a computer
- voice/noise activation
- recording quality should be adjustable (e.g. “talk” and “lecture”)
- 2 AAA batteries allow recording over long periods (e.g. over night)
Recording Conversations
It is advisable that you carry an audio recorder with you at all times and record all conversations that you find threatening, or where you suspect that you will experience harassment, covert messages, references to your private life, or where you have a reason to suspect criminal behaviour.
It is particularly important that you record all conversations with officials, police officers, doctors and psychiatrists. This is crucial because, sadly, there are many examples where these professionals have actively lied to victims or falsified records subsequently.
Notify the Other Party That They Are Being Recorded
Before recording a conversation, you should inform the other party that you are doing so.
In many jurisdictions this is a requirement in order to use the recording in court.
However, if it is a threatening situation, or you feel that the other party will not grant you permission because they are trying to cover up wrongdoing, then it is always better to record covertly than not to record at all. That is because you are trying to prove serious crimes against yourself and (especially in the case of the Secret Services) the other side can behave in extremely criminal, conniving and unpredictable ways.
There are examples where courts permitted the use of covert recordings when they helped to uncover serious wrongdoing.
Covert Recordings
You can do covert recordings even with these rather large and bulky audio recorders by placing them into the front of a rucksack, into its side pocket, into a handbag, or into a jacket pocket. Make sure that the microphone of the audio recorder is facing the opening of the bag and (if the option exists on the device) that the mode of recording is set from “Talk” to “Lecture” or something similar.
The point is that these audio recorders are used to record conversations but also lectures or presentations. For the latter cases the device has a function where noise at a distance is also enhanced for the recording. For covert recordings this mode is ideal because you might not know in advance what might occur around the conversations. The output file is usually larger in that mode.
Storing Records of Conversations
It is important that you backup and store recordings for future reference. That is because it can take a long time to become clear that malpractice has occurred. It is advised that you store the data for several years.
Carry Two and Carry Batteries
Audio recorders are so important that you should carry two at all times if possible. That is because electronic devices are often manipulated from a distance. Experience shows that if one devices is impaired by remote control, the second device is usually not.
Also carry spare batteries, ideally inside the original packaging so that you can quickly tell the difference between new and used batteries.
Audio Recorders Better Than Recording With Mobile Phones
Mobile phones carry microprocessors that are as powerful and multifunctional as laptops were several years ago. This means that a hacked mobile phone can be impaired in many creative ways. In contrast, most audio recorders are rather simple devices that can only record. This means that in many cases they are harder to hack. Thus, making files disappear by remote control is also harder than on a mobile phone.
Furthermore, audio recorders are specialised for the task of recording conversations. The audio quality can be much better than on most mobile phones.
Recording Pulsed Energy Projectiles
Pulsed Energy Projectiles are electromagnetic pulses than can be fired through walls. They are often used by the Secret Services to maim and torture victims inside their home. Measuring electromagnetic pulses is notoriously hard when you don’t know which direction they are being fired from. Specialist equipment that can detect Pulsed Energy Projectiles can be purchased from arms manufacturers but costs several thousand dollars.
One way to do detect and shield from Pulsed Energy Projectiles with little money is to hang long sheets of aluminium foil (baking foil) from the ceiling or drape it around your bed. The impact of an energy projectile on the foil can be audible and sometimes leaves a visible dent in the foil. It has been reported that some shots will punch small holes into the foil.
Attacks with Pulsed Energy Projectiles appear to occur particularly frequently at night when the victims are asleep and therefore helpless. Entire projectile barrages can be heard during those times. Victims report that it sounds “like rain” when the projectiles reflect off the metal surfaces or metal foil. Thus, one way to record such attacks is to drape foil around your bed area (including as a canopy above) and set an audio recorder to record throughout the entire night. 8 hours of high quality recording equate to file sizes of about 400-500MB.
Telephone Pickup Microphone
 |
15 USD from US vendor 20 GBP from UK vendor 25 EUR from German vendor |
- $10 – $25
- allows to record phone conversations, plugs into an audio recorder
- ear piece transmits sound into ear while copying audio to recorder
- NB: Some of these microphones pickup the radiation from cordless telephones (but not mobile phones), which results in background noise on the recording. Should that happen, put the telephone on loud speaker mode and record the conversation with the audio recorder without this ear piece.
Recording phone conversations is just as important as recording real-life conversations. A lot of companies already record our phone calls by default. They announce that they store the data for “quality control and training purposes”. Yes…
In any case, why not do the same? Your “training purposes” might be to train yourself up to spot lying, fraud and sabotage.
Digital Camera (not Wi-Fi enabled!)
 |
109 USD from US vendor 97 GBP from UK vendor 130 EUR from German vendor |
- $100 – $200
- Note: Ensure that it does not have Wifi / WLAN
- Fast capture upon trigger of advantage
- High picture quality at night of advantage
- Storage card of at least 32GB of advantage
It is important that the digital camera does not have Wifi/WLAN to ensure that it cannot be manipulated remotely. The Secret Services still have ways to sabotage the device, however, it is not quite as easy as when they can simply access it via Wifi/WLAN.
Make sure that you photograph or film gang-stalkers whenever you can. This is important because these people are involved in targeted murder and the Secret Services are training these people to form extended networks and active death squads.
Also, photograph (for the court bundle) and film (for further evidence) every incident of sabotage, vandalism or break-ins. If you experience regular break-ins, it might be worth you while to film your flat before you leave your home so that in case of subsequent housebreaking you can show the before-and-after states. This is particularly important if you are alone or if your police service is corrupt.
Power Bank for Cell Phones and Cameras
 |
11 USD from US vendor 17 GBP from UK vendor 14 EUR from German vendor |
- $10 – $20
- Charging of mobile phones and cameras on the go
- Recharge at home, plug devices in when you need power
- USB cable for charging power bank itself and other devices
- Lip-stick sized, fits easily into coat pockets or handbags
- Super handy, so might even carry two
A power bank is an essential tool as it allows to re-charge a mobile phone or digital camera when there is no nearby power socket or the device’s charger is not available. Ensure that you carry a USB cable that has the right connector on the other end for your phone or camera as these might be different.
A power bank is essential for attending protests where police might remotely drain battery power from mobile phones in order to prevent protestors from recording evidence themselves. Sadly, this has been known to happen in the US and Europe. Stalkers related to the Secret Services have also been known to harass their victims by draining their phones.
Should your mobile be drained by such means, move away from the area where the covert devices have affected your phone, then connect your phone to the power bank and recharge it in order to be able to record photo and video evidence.
When mobiles’ battery power is drained remotely, it does not affect the power bank as long as the power bank is not connected to the phone when the latter is drained remotely. This is true, even if the power bank is kept next to the phone in a jacket pocket or a hand bag. The reason for it is that a detached power bank just holds charge, which cannot be dissipated unless a device is connected. In contrast, a phone has an internal processor and if it is remotely “sting-rayed” by the police, they can ramp up the processor’s work load and dissipate the battery power via heat.
Dash-Cam to Record Attacks Driving
 |
146 USD from US vendor 130 GBP from UK vendor 140 EUR from German vendor |
- $50 – $200
- Important to get one with front & rear camera!
- Compatibility with the largest microSD storage cards important (to be able to record long trips).
- Night-vision important.
- Parking-watch mode important.
- Large image resolution important.
- Wide-angle important.
- Ease of dismounting important.
A dash-cam is very important as you might experience targeted attempts to involve you in a car accident or dangerous driving around you. Gang-stalking and threat theatre also happens a lot while driving. Moreover, when being attacked with directed energy weapons, it helps to be able to record the number plates around you on an ongoing basis to collect evidence for court. This is the case even though it is (by design) extremely hard to prove who attacked you.
You don’t actually need to prove who attacked you since you cannot be expected as the victim to do all the forensics yourself. That is the job of the police services and the Intelligence Agencies.
What is important is to get the number plates around you. Then it is obvious that there are money flows and telecommunication connecting the stalkers and attackers from which one can work out which of the cars surrounding you at any one point in time are involved in stalking. As attacks on you driving are part of illegal warfare and crimes against humanity, the investigation will have all the time in the world to work out who the guilty parties were.
Action Cam for Cycling
 |
55 USD from US vendor 30 GBP from UK vendor 50 EUR from German vendor |
- $50 – $150
- Most come with different types of helmet-mounts.
- Very good correcting vibrations during cycling.
- Large microSD card is important for longer trips.
If you cycle regularly for leisure, sport or into work, it is very important to get an action cam and record the trips. Just like when driving a car, stalkers and attackers might try to involve you in a car accident or blame for example the scratching of a scar on you to damage you financially. To avoid this, an action cam can help record the journey. As most models are helmet-mounted, it is also ideal for recording gang-stalkers and street theatre as it will capture anything that you are looking at when you are turning your head.
Webcam
 |
28 USD from US vendor 38 GBP from UK vendor 37 EUR from German vendor |
- $20 – $30
- Plug & Play USB connector, most work as soon as connected
- Can disconnect the camera via the USB cable so you have certainty that it is not on when you don’t expect it to be
- Note: Model shown indicates with a green LED when the camera is on, but this can be overridden by the Secret Services. So you should disconnect the USB to be sure the camera is off.
It is advised that you tape up the camera that is built into your laptop (if your model has such a camera in the frame around the display). Instead use a camera that can be connected via a USB cable. This way, you avoid that the camera is recording you when you don’t want it to record. (Although, be aware that the Secret Services can still record you by other means.)
Note: In principle, the same applies to the in-built microphone of your laptop or computer, however, that is harder to disable as it requires you to open the laptop cover and remove the microphone or damage its connector.
Shielding
Metal Foil (also PEP Detection)
 |
Find extra-strong foil in supermarkets or below 23 EUR from German vendor (extra strong) |
- $2 – $4
- Available in every supermarket.
- The thicker the better.
- Large quantities needed depending on the attacks.
- Copper foils is very good too but much more expensive!
The term “tin-foil” hat was an expression coined by the CIA to discredit those who were trying to protect themselves against the CIA’s early day human experimentation on the American population. The psyop campaign was successful as many people still smugly use the term to discredit victims. By doing so, they betray their lack of understanding of basic physics, which states that electromagnetic waves are reflected at the metal surface.
Alu foil still offer the best protection against attack beams. In the case of burning with microwaves, foil protects completely. With more sophisticated attacks like Pulsed Energy Projectiles (PEP) several layers like 6-8 or more are needed to protect body parts and the foil can be used to make them audible for evidence, see above. Pulsed Energy Shots can punch little holes into the shielding and thereby render it useless. Other wave forms appear to pass through several layers of sheet metal. Back-reflections can also be a problem as modern military weapons like pulsed microwave lasers are so powerful and highly collimated that they can be reflected 100 times and keep beam intensity.
Metal Panels
 |
30 USD from US vendor 30 GBP from UK vendor 12 EUR from German vendor for 0.5mm and 16 EUR for 0.8mm thickness |
- $10 – $30
- Both steel and aluminium are useful for shielding.
- Copper is also useful but very expensive.
- Sizes of 100cm x 60cm and larger are useful as shielding panels.
- Sheet metal is better than metal mesh due to the high frequency and powerful wave forms used in the military assaults.
Sheet metal is not as flexible as aluminium foil but offers better protection due to its thickness. It can be used to build make-shift bunkers and shielded areas, or be placed under bed mattresses to protect from electromagnetic machine-gunning from flats below.
For complete protection against the highest energy Pulsed Energy Projectiles several sheets are required, it appears. As the expense of shielding can be substantial, metal panels are ideal because they can be purchased piece by piece over time as the victims can afford them.
The most common places where one can obtain sheet metal is at DIY stores, building material stores and scrap yards.
Please be careful when handling sheet metal as the edges can be sharp and cause bad cut injuries! Use protective (builder) gloves at all times and fix metal panels securely, especially around sleeping areas!
Metal Shed
 |
480 USD from US vendor 340 GBP from UK vendor 299 EUR from German vendor |
- $300 – $500
- Protection from microwave attacks for work/sleep area.
- Protects against burning and similar forms of mutilation.
- Does not protect against V2K, neurotech and highest-energy Pulsed Energy Projectiles.
- Does protect against some medium intensity Pulsed Energy Projectiles which can be heard as loud impact sounds on the roof and the sides of the shed.
Metal sheds are a good way to protect work areas and sleeping quarters for the most assaulted victims. Microwave burning and a large number of other attack modes are blocked, allowing the victim to rest and work.
Medium-intensity Pulsed Energy Projectile barrage can be made audible as loud impact sounds on the side of the shed. This is excellent for collecting evidence.
While commercially available metal sheds cannot protect against the highest-energy Pulsed Energy Projectiles from military weaponry, it still offers a great amount of protection and relief for victims. The shed can also be used to lean extra metal shielding panels from the outside and inside against the walls for added protection. The roof can be covered with extra shielding panels.
Please note the following:
- V2K, neurotech and implant torture cannot be blocked by metal sheds or even Faraday cages. Sheds are not perfect Faraday cages and even Faraday cages in the form of commercially available nets only offer a certain decibel dampening of electromagnetic raidation.
- When using metal sheds be aware that they are not designed for human inhabitation. Like everything else, it is an emergency measure to protect your life.
- Ensure that you air the metal shed regularly. A shed of the standard size 8 x 6 ft can be used to sleep in for 6-8 hours. It is not advised to sleep in sheds of smaller size with the shed doors closed as the air volume is not enough to provide oxygen for breathing over long periods. The air should be exchanged at regular intervals when working inside any type of shed for longer periods. Ensure that no mould from condensation moisture starts growing on the walls.
- $1000 – $2000
- High quality Faraday Cages tend to be very expensive.
- Needs to be grounded with a clamp connector for full protection.
- $200 – $500
- With key access or electronic number pad
- Can be hidden in furniture, walls or be free standing
- Good line of defence against run-of-the-mill Intel break-ins
- $80 – $400
- Motion detection is important.
- WLAN access means it’s remotely hackable.
- Even without WLAN it can be jammed.
- Continuous filming can show such interruptions.
- $15 – $30
- Can be any colour or shape.
- It is important that it produces bubbles continuously.
- Make sure it can run for hours without overheating.
- $180 (Acousticom 2) – $ 370 (Acoustimeter)
- Both have a of 200 MHz – 8 GHz
- Labelled “Electrosmog Detector” but can detect DEW attacks.
- Units can be V/m (Volts per meter) or μW/m2 (microWatts per square meter). Units do not matter and can be converted.
- EMFields Acousticom 2 & Acoustimeter have an audio output that converts high-frequency signals into audible signals that can be recorded and help to identify the nature of the signal.
- Using the audio output it is easy to identify cordless telephones, mobile phones, WiFi units, remote-controls and some DEW.
- Acousticom2 has a rough and non-linear scale 0.01 – 6 V/m.
- Acoustimeter measures the same range with more sub-divisions.
- $300 – $450
- Gigahertz Solutions HF 35C
- Determines the direction of electromagnetic radiation.
- Frequency band measured: 800 MHz – 2.7 GHz
- Measured power density: 0.1 – 1999 μW/m2
- Very easy to use and light to transport.
- Antenna can be detached.
- Governmental communication TETRA is broadcasting on 380 MHz, so is outside the range.
- LTE and Dvbt broadcast on 450 MHz and are thus also outside the range.
- Device makes HF E35C measures 27 MHz – 2.7 GHz and HF W35C the band 2.6 – 6 GHz.
- $600 – $700
- Spectrum Analyser covering 100 MHz – 4 GHz.
- Allows to analyse the frequency distribution.
- More suitable for advanced investigators.
- Can be connected to computer readout.
- Comes with free readout software.
- $210
- Aceco FC6002MKII RF Tracer has a broad range 1MHz – 6GHz.
- Ideal if not known what frequency the body chips are broadcasting on.
- Very easy to use but needs some care to avoid backgrounds (see below).
- Not suitable for determining which frequency the chips are emitting on (this is essential to find out who has licensed those frequencies).
- Several people have used this device to successfully find RF body implants.
- There are several videos online how to find body implants with this.
- It can also be used to find surveillance bugs in the home, of course.
- Switch off cell phones and other emitters. When trying to detect body implants inside the home, make sure you switch off all cell phones, WLAN routers, take the battery out of cordless telephones and other disconnected emitters, and switch off the main fuse to your home. These types of background radiation emit in the frequency band scanned by the bug detector and can falsify your results. Use a Faraday Cage when scanning yourself in a flat as neighbours’ radiation passes through walls. Ideally you scan yourself in a field or forest, but make sure to check radiation backgrounds using for example the Acousticom 2 above. Note that hidden antennas and radar can cause large backgrounds in the most secluded places. Use a mirror to see the LED display of the device when scanning your head.
- The direction of the antenna is very important. This could be because the small signal generators inside the implants are emitting in certain planes and if the antenna isn’t aligned with the plane of the emitted electromagnetic wave it might not pick it up. So move the bug detector around and try rotating the angle of the antenna above every point. Repeat the measurements as often as you can to really pin down the location of the implants.
- The implants are not emitting continuously. There seem to be several minute intervals between emissions where they go silent and no emissions can be detected. Therefore, be patient and take your time. Sometimes you might have to wait for several minutes. It is best to do the scans repeatedly and at random times to catch the emissions.
- Make sure that the bug detector is well charged. When the battery gets low, there is no indicator on the device to tell you. The bug detector will simply remain silent and not detect anything.
- When the detector locks onto a signal it will detect it even at arms length. The device is manufactured to detect bugs and similar emissions across a very wide range of 1MHz-6GHz (from 1 million Herz to 6 billion Herz). When it finds a strong emission, there seems to be a software algorithm that hones in on the frequency of the source. As a result, when you leave the detector over the location of an implant for longer than 10 seconds, it can happen that when you remove the detector from the source, the alarm keeps going because it has honed in on the signal and can then detect the emissions even half a meter away from the source. (At first, I thought that this is due to backgrounds, but inside a Faraday cage without any backgrounds the effect remained the same. Therefore, it must be a software feature internal to the device.) This means that you have to make sure that the signal disappears entirely for several seconds before starting to look for the next implant to ensure that you don’t mix it up with the alarm from the previous source.
- $ ???
- Allows to determine the precise body chip frequencies.
- Can look up who licensed the frequency to get a list of suspects.
- $500 – $600
- Shows heat generated by chip implants.
- Works out of the box without further setup required.
- Can be used to uncover other hot-spots as well.
- $7 – $20
- Easy to use just like a normal torch.
- Careful not to overexpose yourself, especially your eyes.
- Can detect eye-implants and contamination on surfaces.
- Implants found with UV torches using 385nm and 400nm.
- $150 – $500
- Measures ionising radiation (α, β and γ radiation) & radioactivity
- Does not measure standard electromagnetic radiation.
- Units are μSv/h (microSievert per hour)
- An alert function depending on the radiation level is important.
- Important to be able to set the alarm threshold yourself.
- GammaScout (shown here) records readings and stores them.
- Good devices can connect to a computer and display readings.
- $ ???
- Industrial sites have gas detectors for health and safety.
- Free to use with time-out and adverts.
- $4/month or $34/year without adverts.
- Live display of flight paths of aircraft.
- Some military training flights excluded.
- Global service displaying detail on the local level.
- Can obtain flight number by clicking on aircraft.
Faraday Cage
 |
1000-2000 EUR from German vendor |
Faraday cages offer no protection against Directed Energy Weapon attacks, V2K and most neurotech. However, they can reduce the radiation from conventional sources like radiation from neighbours’ WLAN routers and cell towers.
Security
Home Safe
 |
250 USD from US vendor 200 GBP from UK vendor 209 EUR from German vendor |
While a safe cannot protect your belongings against skilled Intel housebreaking, it serves as a buffer against the regular break-ins which appear to be done for low level harassment and in many cases every time as the victim leaves the house. It can be safely assumed that the Intel agencies have backdoors or other means to break into electronic safes and can also pick standard keys. Nevertheless, a safe helps to prove that the break-ins are of a sophisticated and unusual nature.
You can photograph the safe contents every time before closing the safe. Keep your old logbooks in there. Should one of your logbooks disappear, you have the photo to prove that it was in the safe before and can track down when it disappeared. This creates evidence for court cases that point the finger right back at the Secret Services as no normal burglar would break into a home and then a safe just to remove old logbooks.
Home Surveillance
 |
65 USD for 2 from US vendor 40 GBP from UK vendor 60 EUR from German vendor |
A surveillance system is a good idea to have throughout the night and when you leave the house. There are two types of surveillance camera, wired and wireless. The latter can of course be hacked, but has the advantage that you can sometimes log into the device remotely and check your home when you are out and about. In any case, ensure that your surveillance system has sufficient storage. Individual cameras have local storage of up to 128 GB, if you buy a set of cameras interconnected with a central unit the storage space can be 1TB and higher.
Surveillance camera can be operated either with motion detection and continuously. The former saves on storage space but has the disadvantage that if the motion detection or the operation of the camera is impaired remotely with a jammer then the camera is not going to record anything and you will not know about it. In contrast, if the surveillance camera is recording continuously then there is always something on the image and any interruption in operation will show up in the footage.
The one caveat with continuous surveillance is that a sophisticated trick is to use surveillance footage showing a still image where nothing is happening and using it to overwrite the time window during which an intruder is entering your home. This is a very advanced way of circumventing the surveillance system but is feasible as soon as your surveillance unit can be hacked into remotely, for example because it is connected to the internet or because it communicates with the local base station over WLAN.
Should your attackers be so sophisticated to pull off such a feat and should you have important valuables in your home that warrant extra security precautions one possibility to check the integrity of your surveillance footage is to include a continuous random process that cannot be predicted. For example by including continuously running lava lamps in the frame recorded by your surveillance cameras, see below.
Lava Lamp (for Continuous Surveillance)
 |
21 USD from US vendor 15 GBP from UK vendor 25 EUR from German vendor |
A lava lamp is a not just a fascinating feature or a design gimmick, it can also be used to ensure the integrity of your surveillance footage if you are recording a continuous surveillance video. The idea behind it is the following: While continuous surveillance is the safest type of video surveillance as jamming immediately shows up as an interruption or blacking out of film footage, it comes with the one weakness that it can be overridden by looping surveillance footage. In other words, if your surveillance footage just shows a still image of for example the landing and the entrance door, then several minutes of that still image can be taken and looped to paste over the entry of an intruder.
This is a more advanced trick that intruders can use, but given that most victims are exposed to the full deception arsenal of the Secret Services, it’s not as far fetched as it might seem at first. This is particularly the case if your surveillance system is accessible over WLAN as it can be hacked remotely.
The workaround is to have a lava lamp in the surveillance footage. The lava is forming continuous bubbles in an unpredictable way that is steadily changing due to the turbulence in the fluid generated by the heat. So it becomes very hard to loop footage without there being a significant break in the smooth motion of the rising lava or a sudden change in its size and shape.
The effort involved in detecting such manipulation is of course substantial. However, should you suffer a covert housebreaking in which valuables or important evidence is removed, it can be forensic evidence that is worth gold.
To facilitate this type of forensic cross check make sure that the rising lava in the lamp is clearly visible for the surveillance camera.
Measurement
Electromagnetic Radiation Meter (DEW Attacks)
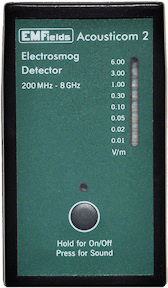 |
Acousticom 180 USD from US vendor 165 GBP from UK vendor 188 EUR from German vendor |
 |
Acoustimeter 370 USD from US vendor 305 GBP from UK vendor 369 EUR from German vendor |
Please put cell phones into airplane/flight mode for measurements as they emit high radiation.
For most victims the cheaper Acousticom 2 is sufficient to detect several different types of DEW attacks. It is important to learn first what miscellaneous types of harmless backgrounds sound like, for example WLAN routers, cordless telephones, remote controls and mobile phones.
The first shocking realisation for most people is to find out how much their mobile phone or WLAN router radiates. Also, the average microwave oven can have enormous radiation leakage. Using this device, it can also be shown that most of the microwave radiation from microwave ovens and WLAN routers can pass through the walls of the home.
With time, very good evidence can be collected with this device. It is recommended that measurements are filmed and that potential sources of very high backgrounds are switched off when using this device (e.g. routers, WiFi/WLAN communication from laptops, mobile phones).
The only downside of this device is that it does not have good directionality in the measurement, so that you cannot detect precisely where the radiation or the electromagnetic pulses are coming from.
The Acousticom and Acoustimeter both measure in the range of 200MHz – 8GHz and have an audio output which you can turn on and off (see the Manual). It is the audio output that is worth gold as it allows you to identify attacks that have been modulated down into the Hertz-range. It is those that are said to interfere with brain functions.
The unit Hertz means simply beats per second. So one beat per second is exactly one Hertz, which you will see written as 1Hz. Two beats per second are two Hertz or 2Hz. One beat every two second is the same as half a beat per second, which is equal to 0.5Hz and so on.
The measurement range of this device starts at 200MHz, which is 200 Mega-Hertz or 200 times 1 million Hertz. This is 200 million beats per second. Similarly, 8GHz is the same as 8 billion beats per second. Humans cannot discern 200 million or 8 billion beats per second.
However, when the attackers use high-frequency waves in the Mega-Hertz (MHz) or Giga-Hertz (GHz) range and modulate the overall signal down into the Hertz range (meaning that they bundle the high-frequency waves into intensity variations that are changing a lot slower) then you can hear it by ear using this device. It will show up as a beat pattern, a knocking or a beeping sound. Signals in the Hertz range you can count by ear. Or if they are a bit too fast for counting, you can use a musical metronome to time them and then read off the beats per second from the metronome.
The advantage of this device because the audio output allows you to detect a very important type of attack that can interfere with your brain function by just listening to the audio.
A lot of the microwave attacks that hurt on the skin and in the joints, show up as a metallic scratching or crackling sound. The best way to describe it is maybe like the sound of metallic crickets. In those cases, it is that metallic sound that allows to identify the microwave beam that is hitting the victim, even though the intensity doesn’t always increase on the display. That is probably the case because the attackers use a main frequency for those attacks that is outside the frequency range of the device but has components that fall within the detectable range.
Directional Radiation Meter (Sources)
 |
435 USD from US vendor 297 GBP from UK vendor 349 EUR from German vendor |
Please put cell phones into airplane/flight mode for measurements as they emit high radiation.
The high frequency measuring device HF 35C manufactured by Gigahertz Solutions is excellent for detecting the radiation of standard everyday devices such as mobile phones, cell towers, microwaves, TV aerials and wireless routers. While the Acousticom and Acoustimeter have a broader frequency range that they measure, this device can help you identify the direction from which radiation is being emitted.
You can use this device to find the location of nearby cell towers and can even check the radiation leaks from kitchen microwaves. What is considered normal in a home, according to a radiation expert, is a level of less than 100 μW/m2. A nearby cell tower should not be hitting your home with around 400-500 μW/m2. You will find that wireless routers and cell phones easily produce radiation far above 2000 μW/m2.
Anything above 1999 μW/m2 is saturating the device and it only shows a “1” at the left hand side of the screen. You should not operate the device in a radiation environment that high for longer than a moment or it can damage the device.
Please note:
Radiation Spectrum Analyser
 |
600 EUR from German vendor |
Please put cell phones into airplane/flight mode for measurements as they emit high radiation.
The Aaronia HF-4040 is a spectrum analyser measuring in the range of 100MHz – 4GHz. The advantage of this device is that you can connect it to a laptop and use the free readout software that comes with the device to record scans over several hours.
A scan samples frequencies in small bands starting at the lower frequency and scanning upwards. You can set the limits of the scan yourself. A full scan from 100MHz to the upper edge of the range at 4GHz takes about 20 seconds. Unlike the previous device, the Aaronia-HF allows one to see individual intensities for every frequency within the range. The antenna allows to hone in on the source. The disadvantage is that one does not have audio output, so spotting down-modulated signals is not possible as such signals appear divided into their individual frequency components. Also, for pulsed signals, it is extremely hard to determine where the signals are coming from.
Bug Detector (RF Body Chips)
 |
170 EUR from German vendor (delivers worldwide) |
The Aceco RF Tracer measures in the region 1MHz-6GHz. You can use it to find illegal implants by scanning the human body for emissions in that range. Human bodies do not emit high frequencies, so if you detect anything it indicates that there is a foreign body inside that is generating the high frequency emissions. See below for a series of videos showing how you can prove your body implants using this device. (Click top right on the list icon to see the entire series of videos.)
To set up the device, turn it on with the button on the top and turn up the dial to maximum to check that a red signal appears on the LEDs on the front. (That is important because when the battery is too low to detect anything, no signal will appear even if the dial is turned to maximum). Then, I would recommend turning the dial back down until the last red bar just about disappears and setting the vibration alarm to ON. That way, an implant in your body that emits at the frequencies the bug finder is sensitive to will immediately show up as a faint or full single bar on the front LEDs. Very strongly emitting implants have two or more LED bars and set off the vibration alarm.
You can show that the emissions are coming from a point of the body by moving the detector repeatedly away from the location where it found a source and demonstrate that the signal immediately disappears when the antenna is not pointing at the source. You can do this 5-10 times and repeat the experiment in different rooms or other locations and you will have ultimate proof that the emission is coming from that point inside the body and not from background sources.
Please note the following:
Frequency Counter (WANTED!!! Body Chip Frequencies)
 |
USD from US vendor GBP from UK vendor EUR from German vendor |
Measuring the precise frequencies upon which the radio-frequency emitting body implants are broadcasting allows one to look up who has licensed those frequencies. The licences are usually held by the military, research universities and so called “high net-worth individuals”. The list of licence holders is the list of suspects who are running the criminal human experimentation and brutal torture of the victims.
NO GOOD FREQUENCY COUNTER HAS BEEN FOUND YET THAT ALLOWS TO DETERMINE THE CHIP FREQUENCIES RELIABLY.
If you can recommend such a device please get in touch with Dr. Horton via email using contact@stop007.org.
Thermal Camera (Body Implants, Weapons)
 |
499 USD from US vendor 610 GBP from UK vendor 595 EUR from German vendor |
 |
The Joint Investigation Team has a measurement from a prominent victim that shows several head chips clearly on an image taken with the FLIR C2 camera.
Note: The C3 is more expensive, yet has the same measurement performance as the C2, with the only extra feature being Wi-Fi connectivity. In the case of Secret Service victims it is advised to avoid Wi-Fi as it can be remotely interfered with.
It should be noted that not all body implants show up on thermal images. This is just an extra mode of detection. The chips which can be seen are for example body chips that generate a significant amount of heat through intense operation or from high currents being generated to cause intense pain sensations.
Thermal cameras have also been used by victims to show weapons hidden behind walls at neighbours. What the camera shows is the heat generated by the weapon and the microwave radiation that passes through the wall. Using this type of camera hidden weapons become visible.
UV Torch (Eye Implants, Contamination)
 |
10 USD from US vendor 6 GBP from UK vendor 7 EUR from German vendor |
Ultraviolet light, also known as black light, can be used to detect contamination on furniture, carpets, clothes and household objects. However, it can also reveal one of the most cruel and insidious covert implants used by the Secret Services: eye implants consisting of transparent thin-film technology placed on the lens of the eye with a small readout module typically above the iris under the eye-lid. Eye implants have been found using UV light torches emitting 385nm to 400nm.
Shine the UV light from a distance onto your face, if your iris and pupils reflect in an unusual colour like turquoise, purple or show up as milky, it is an indication that a thin-film layer has been placed on your eye as synthetic technology reflects light in a different colour to human eyes.
Don’t shine UV light directly into your eye! Limit time of exposure. Don’t try to remove eye implants yourself! Implants attach to eye tissue and cause damage. See an ophthalmologist!
Here is an example for a victim who has experienced eye-implant based harassment and appears to have found an eye-implant using an ultra-violet light torch. Both eyes showed the same effect shown below.
 |
Victim’s eye under normal light. |
 |
The same eye under ultra-violet light showing purple and turquoise reflections on the iris and the pupil typical of thin-film technology based eye implants. |
Geiger Counter (Radioactivity, X-Ray Surveillance)
 |
489 USD from US vendor 338 GBP from UK vendor 399 EUR from German vendor |
The device that measures radioactivity is called a good Geiger counter. It can be expensive but lasts for years. The normal background of naturally occurring radiation in most places on Earth is about 0.1 – 0.2 μSv/h. When exposed to X-ray imaging for surveillance purposes, there are short bursts of much higher radioactivity. The precise dosage measured depends on the amount of building material between the victim and the X-ray emitter but typically there are short bursts of very high radioactivity 400-1500 times above ambient backgrounds, i.e. at around 80 – 150 μSv/h or higher.
Attacks with radioactivity are not typically complained about by victims, but they are that much more insidious because they do occur but go unnoticed. Unlike electromagnetic waves that can cause burning and pain, attacks with ionising radiation are not felt unless the victim begins to suffer the severe effects of so called radiation poisoning which can be devastating and even lethal.
It is well known from the aftermath of the nuclear bombs dropped around the world and nuclear reactor disasters like Chernobyl that ionising radiation and radioactivity can cause cancer, other health effects, genetic damage and death. The murder of the Russian Alexander Litvinenko in London through what was said to be poisoning with highly radioactive polonium-210 shows that the Secret Services do employ radioactivity to destroy and kill their victims.
For this reason, it is important that targets start collecting data about the radioactivity that they are exposed in their homes and outdoors. This is crucial since X-rays are used in surveillance freely and completely unregulated.
Unknown to most people, border crossings have large X-ray devices that can scan entire buses and lorries at once. The author has seen an image showing a large bus filled with sitting skeletons as the passengers received a full-body X-ray without their knowledge. The author was exposed herself to very high X-ray radiation as her car was scanned by a surveillance patrol. In America, the existence and patrolling of cities by X-ray surveillance vans has been openly published in the press.
While this type of irradiation is such a severe health hazard that it requires strict regulation and monitoring in the health industry, it is completely unregulated when used by a much more uneducated and statistically speaking highly psychopathic segment of society: the police, the military and the Secret Services. The outcome of that is clear. It results in prolific and wanton mutilation of the civilian population which is entirely oblivious to the operation and abundant use of X-ray surveillance equipment affecting themselves and their children. Plans to make round-the-clock X-ray surveillance of cities the norm around the world contributes to soaring cancer deaths.
Gas Detector (Gas Poisoning)
 |
USD from US vendor GBP from UK vendor EUR from German vendor |
NO GOOD AFFORDABLE GAS DETECTOR HAS BEEN FOUND YET THAT ALLOWS TO DETERMINE GAS POISONING RELIABLY.
If you can recommend such a device please get in touch with Dr. Horton via email using contact@stop007.org.
|
|
USD from US vendor GBP from UK vendor EUR from German vendor |
Data Collection
Social Media Logs
Many victims receive threats and abusive messages from online abusers via social media and other online communication platforms. The documents leaked by Edward Snowden revealed that Intelligence Agencies like GCHQ in the UK hire entire troll factories to terrorise victims.
Should you have suffered such abuse, you can uncover the identity of the abusers. The social media platform’s network log should have a record of the IP address that was used to send the abusive messages. You should subpoena that information from the social media company.
What you need in order to request that information is the username that sent the abusive messages, the date and time the message was sent and, if available, the identification number of the social media post. For example in the case of Twitter, click on the abusive Twitter message and copy the URL that appears in the browser’s address bar when you select the abusive message. This should contain the user name and the tweet’s identification number as the last part of the URL, as shown here:
https://twitter.com/username/status/1027317784185921534
It is also important to screenshot the abusive message. Ideally, the screenshot should also show the URL and the date and time displayed for example on your desktop. This gives you an additional handle on the timestamp.
Flight Radar
 |
Flight Radar 24 |
Many people report noise harassment, targeted assaults with Directed Energy Weapon and stalking by helicopters and other aircraft. Flight logs have to be kept on all aircraft by law and Flight Radar 24 is an online service that allows to display the live flight paths of all aircraft, except military flights.
Victims can look up the exact flight number on this website and thereby identify the aircraft that might be involved in vexatious behaviour or launching Directe Energy Weapon assaults. Circling movement of helicopters around certain communities can also be made visible by recording a video of the computer screen displaying this website, or by taking multiple screenshots that show the position of aircraft with time.
Tip: When taking screenshots or making video screen recordings on your computer, try to take it such that the date and time display on your desktop is visible. This gives an extra indication of when you recorded the footage in addition to the time stamp on the output file itself.